overleaf template galleryLaTeX templates and examples — Recent
Discover LaTeX templates and examples to help with everything from writing a journal article to using a specific LaTeX package.
Este es el formato que usé para graduarme del PCCM
Nitin Bawane's Computer Science Resume. Created with the Modern CV template.
This template is for computational project/lab reports for basic science classes such as Physics, Math and Differential Equations.
Arquivo que representa um modelo de relatório em LaTeX, desenvolvido para ser utilizados nas disciplinas de laboratório no Curso Superior de Tecnologia em Automação Industrial.
Formato simple para presentar reportes de prácticas. Útil para las carreras de Ingeniería Fotónica, Ingeniería Electrónica, Ingeniería en Computación, Ingeniería en Robótica y cualquier área afín a estas.
Bachelor's thesis template for Manipal Institute of Technology. Created and Maintained (2019-) by: Avnish Sachar Department of Mechatronics Engineering Manipal Institute of Technology Manipal Academy of Higher Education E-mail: avnishsachar2@gmail.com
Plantilla sencilla para la realización de Trabajos de Fin de Grado en la Escuela Técnica Superior de Ingenieros de Sistemas Informáticos (Universidad Politécnica de Madrid) Está dirigida a los estudiantes que tienen una experiencia limitada con LaTeX o que no deseen realizar una memoria desde 0.
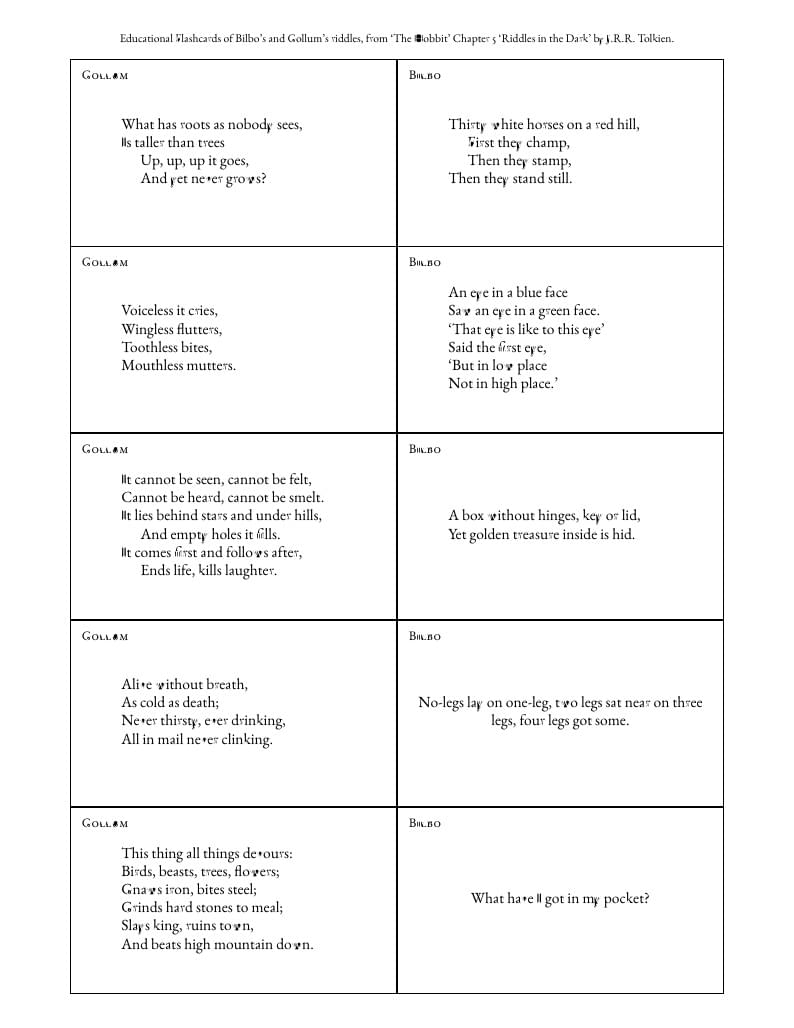
Flashcards of Bilbo's and Gollum's riddles, from ‘The Hobbit’ Chapter 5 ‘Riddles in the Dark’, using the flashcards and verse packages.
SAR image clustering
\begin
Discover why over 25 million people worldwide trust Overleaf with their work.